Abstract
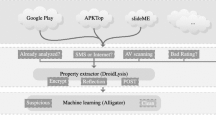
Spotting malicious samples in the wild has always been difficult, and Android malware is no exception. Actually, the fact Android applications are (usually) not directly accessible from market places hardens the task even more. For instance, Google enforces its own communication protocol to browse and download applications from its market. Thus, an efficient market crawler must reverse and implement this protocol, issue appropriate search requests and take necessary steps so as not to be banned. From end-users’ side, having difficulties spotting malicious mobile applications results in most Android malware remaining unnoticed up to 3 months before a security researcher finally stumbles on it. To reduce this window of opportunity, this paper presents a heuristics engine that statically pre-processes and prioritizes samples. The engine uses 39 different flags of different nature such as Java API calls, presence of embedded executables, code size, URLs… Each flag is assigned a different weight, based on statistics we computed from the techniques mobile malware authors most commonly use in their code. The engine outputs a risk score which highlights samples which are the most likely to be malicious. The engine has been tested over a set of clean applications and malicious ones. The results show a strong difference in the average risk score for both sets and in its distribution, proving its use to spot malware.
Similar content being viewed by others
References
Anderson, C., Wolff, M.: The web is dead. Long live the internet. (2010). http://www.wired.com/magazine/2010/08/ff_webrip/all/1
Apvrille, A., Zhang, J.: Four malware and a funeral. In: 5th Conf. on Network architectures and information systems security (SAR-SSI) (2010)
Armstrong, T., Maslennikov, D.: Android malware is on the rise. In: Virus bulletin conference (2011)
Bläsing, T., Schmidt, A.-D., Batyuk, L., Camtepe, S.A., Albayrak, S.: An Android application sandbox system for suspicious software detection. In: 5th international conference on malicious and unwanted software (MALWARE’2010). Nancy, France (2010)
Cannon, T.: No-permission Android App Gives Remote Shell. (2011). http://viaforensics.com/security/nopermission-android-app-remote-shell.html
Ikinci, A., Holz, T., Freiling, F.C.: Monkey-spider: detecting malicious websites with low-interaction honeyclients. In: Sicherheit, pp. 407–421 (2008)
Logan, R., Desnos, A., Smith, R.: The Android marketplace Crawler (2011). http://www.honeynet.org/gsoc/ideas
Lookout mobile security: lookout mobile threat report (2011)
Ma, J., Saul, L.K., Savage, S., Voelker, G.M.: Beyond blacklists: learning to detect malicious web sites from suspicious urls. In: Proceedings of the 15th acm sigkdd international conference on knowledge discovery and data mining, pp. 1245–1254. ACM, New York (2009)
McAffee Labs.: Mc Affee threats report: third quarter 2011 (2011). http://www.mcafee.com/us/resources/reports/rp-quarterly-threat-q3-2011.pdf
Pišljar, P.: Reversing Android market protocol (2010). http://peter.pisljar.si/
de Pontevès, K.: Android Malware Surges in 2011 (2011). https://blog.fortinet.com/android-malware-surges-in-2011
Protocol Buffers.: (n.d.). http://code.google.com/p/protobuf/
Schmidt, A.-D., Schmidt, H.-G., Batyuk, L., Clausen, J.H., Camtepe, S.A., Albayrak, S.: Smartphone malware evolution revisited: Android next target? In: 4th international conference on malicious and unwanted software (malware), IEEE, pp. 1–7 (2009)
Smali.: (n.d.). https://code.google.com/p/smali
Strazzere, T.: Downloading market applications without the Vending app. (2009). http://strazzere.com/blog/?p=293
Teufl, P., Kraxberger, S., Orthacker, C., Lackner, G., Gissing, M., Marsalek, A., et al.: Android market analysis with activation patterns. In: Proceedings of the international ICST conference on security and privacy in mobile information and communication (MobiSec) (2011)
Wang, Y.-M., Beck, D., Jiang, X., Roussev, R., Verbowski, C., Chen, S., et al.: Automated web patrol with strider honeymonkeys: finding web sites that exploit browser vulnerabilities. In: Proceedings of the network and distributed system security symposium, NDSS 2006, San Diego, California, USA. The Internet Society (2006)
Wikipedia: Android Market (2011). https://en.wikipedia.org/wiki/Android_Market
Zhou, Y., Wang, Z., Zhou, W., Jiang, X.: Hey, you, get off of my market: detecting malicious apps in official and alternative android markets. In: Proceedings of the 19th network and distributed system security symposium (NDSS 2012), San Diego, CA (2012)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Apvrille, A., Strazzere, T. Reducing the window of opportunity for Android malware Gotta catch ’em all. J Comput Virol 8, 61–71 (2012). https://doi.org/10.1007/s11416-012-0162-3
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11416-012-0162-3