Abstract
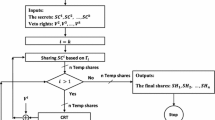
Traditional secret sharing assume the absolute secrecy of the private shares of the uncorrupted users. It may not hold in the real world due to the side-channel attacks. Leakage-resilient cryptography is proposed to capture this situation. In the continual leakage model, the attacker can continuously leak the private value owned by the user with the constraint that the information leaked should be less than ℓ between updates. We propose continual leakage-resilient dynamic secret sharing under split-state model in this paper. After a preprocessing stage, the dealer is able to dynamically choose a set of n users and to allow a threshold of t users to reconstruct different secrets in different time instants, by using the same broadcast message. The secrets are protected even if an adversary corrupts up to t − 1 users and obtains continual leakage from the rest of them. Our scheme can provide the security for secret sharing under continual leakage model while at the same time allowing the users to join and quit the scheme dynamically.
Chapter PDF
Similar content being viewed by others
References
Akavia, A., Goldwasser, S., Vaikuntanathan, V.: Simultaneous Hardcore Bits and Cryptography against Memory Attacks. In: Reingold, O. (ed.) TCC 2009. LNCS, vol. 5444, pp. 474–495. Springer, Heidelberg (2009)
Blakley, B., Blakley, G.R., Chan, A.H., Massey, J.L.: Threshold Schemes with Disenrollment. In: Brickell, E.F. (ed.) CRYPTO 1992. LNCS, vol. 740, pp. 540–548. Springer, Heidelberg (1993)
Blundo, C., Cresti, A., De Santis, A., Vaccaro, U.: Fully Dynamic Secret Sharing Schemes. In: Stinson, D.R. (ed.) CRYPTO 1993. LNCS, vol. 773, pp. 110–125. Springer, Heidelberg (1994)
Boneh, D., Boyen, X., Goh, E.-J.: Hierarchical Identity Based Encryption with Constant Size Ciphertext. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 440–456. Springer, Heidelberg (2005)
Boyle, E., Goldwasser, S., Kalai, Y.T.: Leakage-Resilient Coin Tossing. In: Peleg, D. (ed.) DISC 2011. LNCS, vol. 6950, pp. 181–196. Springer, Heidelberg (2011)
Brakerski, Z., Kalai, Y.T., Katz, J., Vaikuntanathan, V.: Overcoming the hole in the bucket: Public-key cryptography resilient to continual memory leakage. In: FOCS, pp. 501–510. IEEE Computer Society (2010)
Davì, F., Dziembowski, S., Venturi, D.: Leakage-Resilient Storage. In: Garay, J.A., De Prisco, R. (eds.) SCN 2010. LNCS, vol. 6280, pp. 121–137. Springer, Heidelberg (2010)
Delerablée, C., Pointcheval, D.: Dynamic Threshold Public-Key Encryption. In: Wagner, D. (ed.) CRYPTO 2008. LNCS, vol. 5157, pp. 317–334. Springer, Heidelberg (2008)
Dodis, Y., Lewko, A.B., Waters, B., Wichs, D.: Storing secrets on continually leaky devices. In: Ostrovsky, R. (ed.) FOCS, pp. 688–697. IEEE (2011)
Laih, C.-S., Harn, L., Lee, J.-Y., Hwang, T.: Dynamic Threshold Scheme Based on the Definition of Cross-Product in an N-dimensional Linear Space. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 286–298. Springer, Heidelberg (1990)
Lewko, A.B., Rouselakis, Y., Waters, B.: Achieving Leakage Resilience through Dual System Encryption. In: Ishai, Y. (ed.) TCC 2011. LNCS, vol. 6597, pp. 70–88. Springer, Heidelberg (2011)
Scott, M.: Authenticated id-based key exchange and remote log-in with simple token and pin number. Cryptology ePrint Archive, Report 2002/164 (2002), http://eprint.iacr.org/
Shamir, A.: How to share a secret. Commun. ACM 22(11), 612–613 (1979)
Yuen, T.H., Chow, S.S.M., Zhang, Y., Yiu, S.M.: Identity-Based Encryption Resilient to Continual Auxiliary Leakage. In: Pointcheval, D., Johansson, T. (eds.) EUROCRYPT 2012. LNCS, vol. 7237, pp. 117–134. Springer, Heidelberg (2012)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2012 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Xiong, H., Zhang, C., Yuen, T.H., Zhang, E.P., Yiu, S.M., Qing, S. (2012). Continual Leakage-Resilient Dynamic Secret Sharing in the Split-State Model. In: Chim, T.W., Yuen, T.H. (eds) Information and Communications Security. ICICS 2012. Lecture Notes in Computer Science, vol 7618. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-34129-8_11
Download citation
DOI: https://doi.org/10.1007/978-3-642-34129-8_11
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-34128-1
Online ISBN: 978-3-642-34129-8
eBook Packages: Computer ScienceComputer Science (R0)