Abstract
We revisit the question of whether cryptographic protocols can replace correlated equilibria mediators in two-player strategic games. This problem was first addressed by Dodis, Halevi and Rabin (CRYPTO 2000), who suggested replacing the mediator with a secure protocol and proved that their solution is stable in the Nash equilibrium (NE) sense, provided that the players are computationally bounded.
We show that there exist two-player games for which no cryptographic protocol can implement the mediator in a sequentially rational way; that is, without introducing empty threats. This explains why all solutions so far were either sequentially unstable, or were restricted to a limited class of correlated equilibria (specifically, those that do not dominate any NE, and hence playing them does not offer a clear advantage over playing any NE).
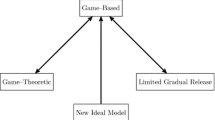
In the context of computational NE, we classify necessary and sufficient cryptographic assumptions for implementing a mediator that allows to achieve a given utility profile of a correlated equilibrium. The picture that emerges is somewhat different than the one arising in semi-honest secure two-party computation. Specifically, while in the latter case every functionality is either “complete” (i.e., implies Oblivious Transfer) or “trivial” (i.e., can be securely computed unconditionally), in the former there exist some “intermediate” utility profiles whose implementation is equivalent to the existence of one-way functions.
Supported by the European Research Commission Starting Grant 279447, ISF grant no. 334/08, and Danish National Research Foundation and The National Science Foundation of China (grant 61061130540) for the Sino-Danish Center for the Theory of Interactive Computation.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Atallah, M.J., Blanton, M., Frikken, K.B., Li, J.: Efficient correlated action selection. In: Di Crescenzo, G., Rubin, A. (eds.) FC 2006. LNCS, vol. 4107, pp. 296–310. Springer, Heidelberg (2006)
Aumann, R.J.: Subjectivity and correlation in randomized strategies. Journal of Mathematical Economics 1(1), 67–96 (1974)
Aumann, R.J., Hart, S.: Long cheap talk. Econometrica 71(6), 1619–1660 (2003)
Bárány, I.: Fair distribution protocols or how the players replace fortune. Mathematics of Operations Research 17(2), 327–340 (1992)
Canetti, R.: Universally composable security: A new paradigm for cryptographic protocols. IACR Cryptology ePrint Archive 2000, 67 (2000)
Crépeau, C., Morozov, K., Wolf, S.: Efficient unconditional oblivious transfer from almost any noisy channel. In: Blundo, C., Cimato, S. (eds.) SCN 2004. LNCS, vol. 3352, pp. 47–59. Springer, Heidelberg (2005)
Dodis, Y., Halevi, S., Rabin, T.: A cryptographic solution to a game theoretic problem. In: Bellare, M. (ed.) CRYPTO 2000. LNCS, vol. 1880, pp. 112–130. Springer, Heidelberg (2000)
Farrell, J., Rabin, M.: Cheap talk. The Journal of Economic Perspectives 10(3), 103–118 (1996)
Gradwohl, R., Livne, N., Rosen, A.: Sequential rationality in cryptographic protocols. In: FOCS, pp. 623–632. IEEE Computer Society (2010)
Groce, A., Katz, J.: Fair computation with rational players. In: Pointcheval, D., Johansson, T. (eds.) EUROCRYPT 2012. LNCS, vol. 7237, pp. 81–98. Springer, Heidelberg (2012)
Impagliazzo, R.: A personal view of average-case complexity. In: Structure in Complexity Theory Conference, pp. 134–147 (1995)
Impagliazzo, R., Luby, M.: One-way functions are essential for complexity based cryptography (extended abstract). In: FOCS, pp. 230–235. IEEE Computer Society (1989)
Maji, H.K., Prabhakaran, M., Sahai, A.: On the computational complexity of coin flipping. In: FOCS, pp. 613–622. IEEE Computer Society (2010)
Nash, J.: Non-cooperative games. Annals of Mathematics 54(2), 286–295 (1951)
Osborne, M.J., Rubinstein, A.: A course in game theory. MIT Press (1994)
Pass, R., Shelat, A.: Renegotiation-safe protocols. In: Chazelle, B. (ed.) ICS, pp. 61–78. Tsinghua University Press (2011)
Teague, V.: Selecting correlated random actions. In: Juels, A. (ed.) FC 2004. LNCS, vol. 3110, pp. 181–195. Springer, Heidelberg (2004)
Teague, V.: Problems With Coordination in Two-Player Games: Comment on ”Computational Complexity and Communication”. Econometrica 76(6), 1559–1564 (2008)
Urbano, A., Vila, J.E.: Computational complexity and communication: Coordination in two–player games. Econometrica 70(5), 1893–1927 (2002)
Wolf, S., Wullschleger, J.: Zero-error information and applications in cryptography. In: Information Theory Workshop, pp. 1–6. IEEE (October 2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 International Association for Cryptologic Research
About this paper
Cite this paper
Hubáček, P., Nielsen, J.B., Rosen, A. (2013). Limits on the Power of Cryptographic Cheap Talk. In: Canetti, R., Garay, J.A. (eds) Advances in Cryptology – CRYPTO 2013. CRYPTO 2013. Lecture Notes in Computer Science, vol 8042. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40041-4_16
Download citation
DOI: https://doi.org/10.1007/978-3-642-40041-4_16
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40040-7
Online ISBN: 978-3-642-40041-4
eBook Packages: Computer ScienceComputer Science (R0)